Protecting sensitive information in today's digital landscape is a challenge. Conducting a thorough information security risk assessment (ISRA) or Cyber Security Risk Assessment (CSRA) is crucial for any Australian organisation seeking to proactively identify, analyse, and prioritise potential threats to its data assets. This guides provides a cyber security risk sources overview and delves into the diverse risk sources you should consider during your cyber risk assessment, drawing insights from established frameworks including:
- SP 800-30 Rev. 1 Guide for Conducting Risk Assessments
- ISO 27001 Annex A
- ISO 27005: Guidance on managing information security risks
- Cybersecurity & Data Privacy Risk Management Model (C|P-RMM)
An analysis of recent cyberattacks in Australia and threat reports can help you identify potential vulnerabilities in your organisation's IT infrastructure and implement appropriate security measures:
Cyber security risk sources overview - Fundamental concepts
Before diving into specific sources, it's essential to grasp the fundamental concepts of information security risk. SP 800-30 defines it as "the combination of the probability of an occurrence of an undesirable event (threat) and the consequences of that event." In simpler terms, risk = likelihood of an attack x impact of the attack. Therefore, a comprehensive ISRA involves identifying potential threats, assessing their likelihood of occurrence, and evaluating the potential harm they could inflict on your organisation.
Considerations And Information Security Risk Sources
Step 1: Concider threats:
External, malicious actors like cybercriminals, hacktivists, and nation-states pose a constant threat. The ASD Cyber Threat Report 2022-2023 highlights ransomware, data breaches, and supply chain attacks as critical concerns. Internal, unintentional or malicious actions by employees, contractors, or third-party vendors can compromise security. Consider disgruntled employees, human error, and social engineering attacks. Physical threats such as natural disasters, fires, power outages, and equipment failures can disrupt operations and data availability. These fall under the "environmental disruptions" category in SP 800-30.
Step 2: Understand your vulnerabilities:
System vulnerabilities such as unpatched software, outdated systems, and misconfigurations create exploitable weaknesses. SCF Risk & Threat Catalog offers a structured approach to identifying such vulnerabilities. Process issues such as weak access controls, inadequate data encryption, and lack of incident response plans introduce process-related vulnerabilities. Refer to ISO 27001 Annex A for best practices in managing these. Also concider the human factor, such as lack of awareness, poor security practices, and susceptibility to social engineering attacks are human factors contributing to risk. ISO 27005 emphasises the importance of security awareness training.
Step 3: Identify your assets:
Data, such as customer information, financial records, intellectual property, and other sensitive data are prime targets for attackers. Classify your data based on its confidentiality, integrity, and availability requirements. System components such as servers, databases, applications, and network devices are potential attack vectors. Consider their security controls and patching procedures.And physical locations housing critical infrastructure require physical security measures like access control and environmental monitoring.
Step 4: Confirm compliance:
Failing to comply with relevant data privacy and security regulations like GDPR or HIPAA can lead to financial penalties and reputational damage. SP 800-30 emphasises legal and regulatory requirements as part of the risk assessment process. Internal policies and procedures such as organisational policies on data handling, password management, and acceptable use govern internal controls and contribute to mitigating risk.
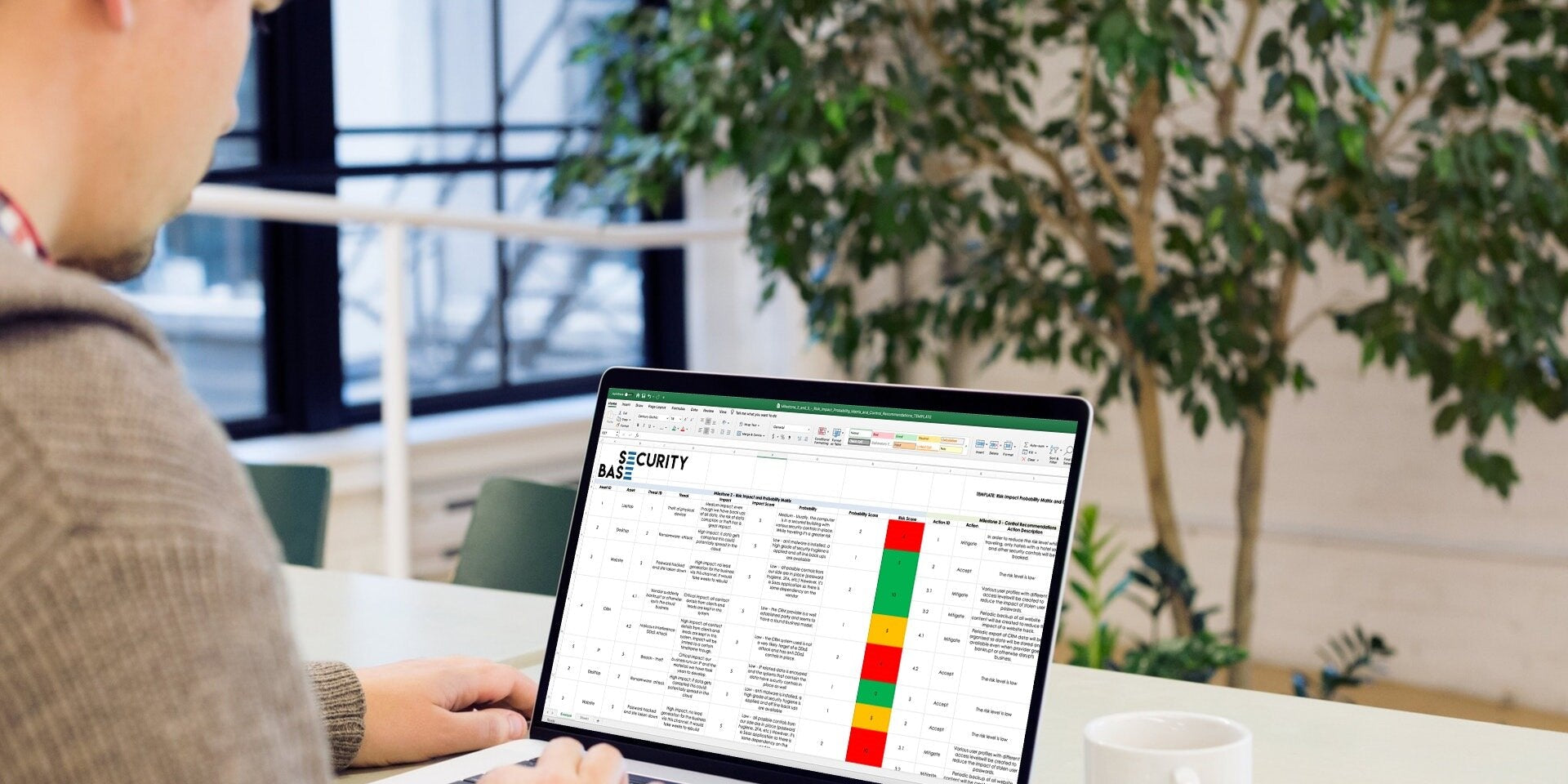
Conducting An Information Security Risk Assessment
You can create a robust ISRA methodology by combining insights from these frameworks and reports. Here are some key steps:
- Identify assets and their value: This lays the foundation for understanding what needs protection.
- Catalogue threats and vulnerabilities: Leverage resources like SCF Risk & Threat Catalog and the ASD Cyber Threat Report to stay updated.
- Assess likelihood and impact: Evaluate the probability of each threat exploiting a vulnerability and the potential consequences.
- Prioritise risks: Focus resources on mitigating the highest-impact risks first.
- Develop mitigation strategies: Implement technical, procedural, and training measures to address identified risks.
- Continuously monitor and update: Regularly review and update your ISRA as your environment and threats evolve.
Navigating the ever-changing information security landscape requires a proactive approach. By adopting a comprehensive ISRA methodology informed by established frameworks and reports, you can effectively identify, prioritise, and mitigate risks, safeguarding your valuable data assets and ensuring business continuity. Remember, information security is not a one-time event but an ongoing process requiring continuous vigilance and adaptation.