With microphones built into many devices, people worry about them on their phones, laptops, and other equipment. And this can be for good reasons as microphones are hacked by North Korean hack syndicates, concerns are raised by security bloggers and the Australian Cyber Security Centre has a guideline to prevent hacking of audio devices.
But can you disable them with a microphone blocker? Like many things in cybersecurity, the answer is a nuanced "it depends." This post explores the challenges and potential solutions for silencing your microphone, empowering you to take back control of your privacy.
Software Solutions: Limited Effectiveness
While turning off the microphone through software settings on your device might seem straightforward to protect your privacy, this approach has limitations. It often only restricts access to standard applications. Malicious apps or those with overly broad permission requests could still access the microphone.
Even with the microphone muted, sophisticated malware or exploits might leverage software vulnerabilities to gain unauthorised access. Some mobile devices have pre-installed apps or functionalities with built-in microphone access, regardless of user settings. While these might be legitimate features, their existence highlights the limitations of software-based solutions. For a more robust layer of security, combining software-based disabling with user awareness and potentially hardware blockers is recommended.
Testing And Monitoring: Tools For Enhanced Security
Verifying successful microphone deactivation requires a multifaceted approach. Basic audio recording software can confirm the absence of captured audio. Advanced users can leverage tools capable of analysing subsonic and ultrasonic ranges, potentially uncovering covert communication channels and sophisticated spyware use.
System monitoring applications, such as "Micro Snitch" for macOS, can provide real-time alerts whenever an application attempts to access the microphone. This enables users to identify and potentially mitigate unauthorised access attempts.
The Biggest Risk: "Smart" Devices
Smart home devices equipped with voice-activated assistants pose a unique challenge. These devices often rely on multiple microphones for optimal functionality, and software-based disabling might only partially prevent audio capture. Vulnerabilities or external hacking attempts could activate microphones even when users believe they are disabled.
A two-pronged approach is recommended for smart devices: physical microphone removal for users with extreme security concerns or a heightened level of trust in the device manufacturer's security practices.
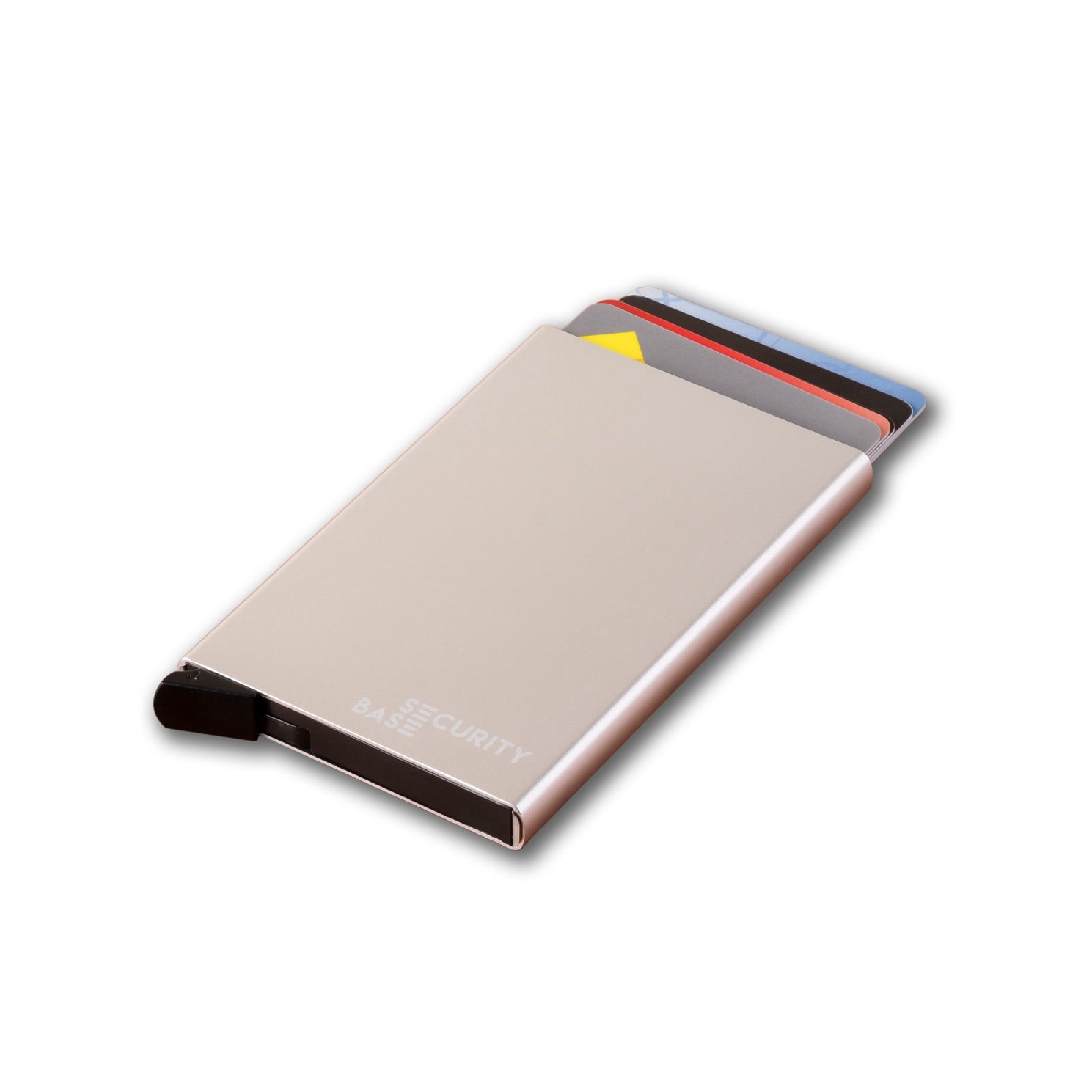
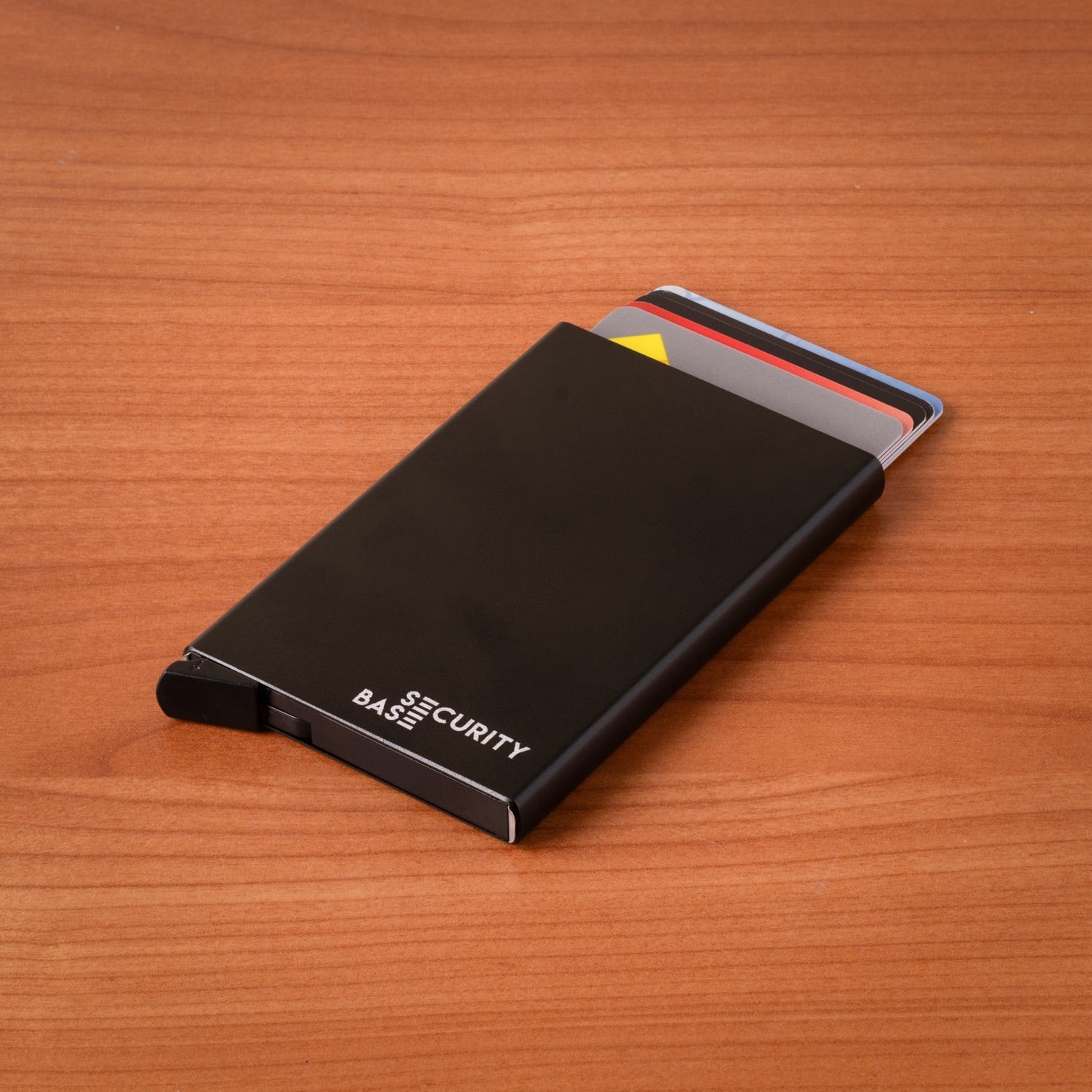
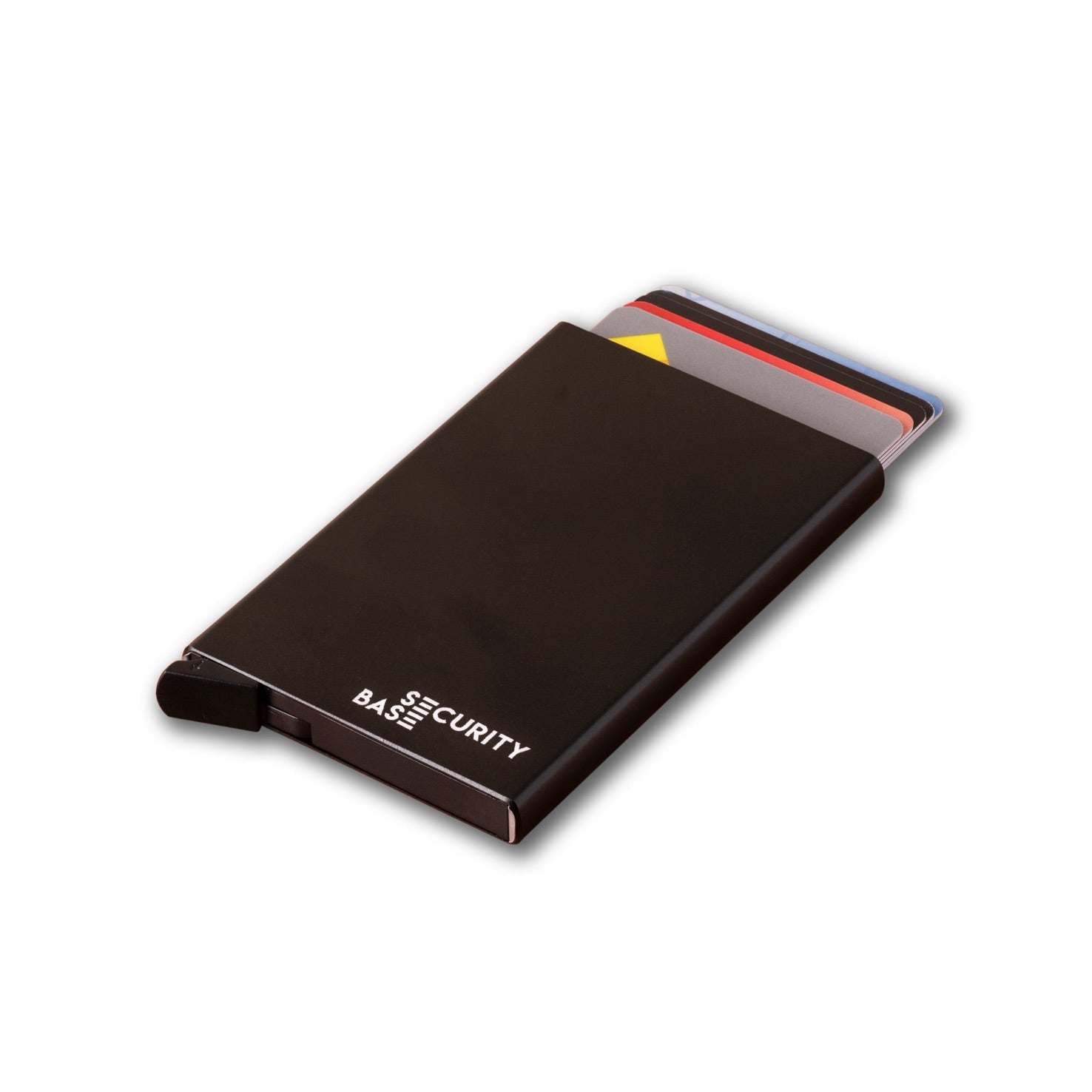
Hardware Solutions: Microphone Blockers
Microphone blockers offer a convenient option for an additional layer of physical security. Microphone blockers provide a solution for computers and phones. These create a fake microphone that apps can access but doesn't capture any sound. These small yet powerful privacy devices come in two main varieties:
- Hardware Microphone Blockers typically connect to the standard 3.5mm headphone jack, creating a physical barrier between the microphone and any potential eavesdroppers. They are a simple and effective solution for laptops and desktops.
- Wireless Microphone Blockers use Bluetooth or Wi-Fi to turn off the microphone signal wirelessly. This option is suitable for everyone seeking a versatile solution across multiple devices. These innovative devices utilise Bluetooth technology to block the microphone signal remotely. This approach provides greater flexibility, allowing you to secure microphones on laptops, tablets, and even some smart devices.
A Layered Approach to Microphone Security
Disabling microphones effectively hinges on the specific device and the security posture you wish to establish. Implementing a combination of software-based testing and monitoring tools, coupled with a microphone blocker for additional physical security, empowers users to create a layered defence against unauthorised microphone access. Remember, a vigilant approach forms the cornerstone of a robust privacy strategy.