The Security Concerns of RFID Technology
Radio-frequency identification (RFID) technology has revolutionised the way we live, work, and interact with the world around us. From contactless payments and access control systems to inventory management and supply chain tracking, RFID is ubiquitous in our daily lives. This technology utilises electromagnetic fields to automatically identify and track tags attached to objects. While offering numerous benefits, RFID also presents significant security concerns, particularly the vulnerability to RFID hacking.
RFID tags, which are small, passive devices that contain a unique identifier and other data, can be susceptible to unauthorised access. Hackers can employ specialised equipment to read the information stored on an RFID tag, potentially compromising sensitive personal data such as credit card numbers, passport details, or even medical records. This type of attack, known as RFID hacking, can have serious consequences for individuals and businesses alike.
Understanding the Risks of RFID Hacking
The widespread adoption of RFID technology has made it a prime target for malicious actors. RFID hacking can take various forms, including:
- Skimming: Hackers use specialised devices such as the Flipper Zero to intercept the radio signals emitted by RFID tags, allowing them to capture sensitive data without the owner's knowledge. These devices, often disguised as ordinary objects like card readers or even mobile phone cases, can discreetly capture the data transmitted by RFID tags, making it particularly challenging to detect.
- Relay Attacks: In this type of attack, hackers intercept the communication between an RFID tag and a reader, impersonating the legitimate reader to gain access to the tag's data. Hackers can use a relay device to capture the signal from the tag and then transmit it to a fake reader, allowing them to access the information stored on the tag. This attack can be particularly effective in environments with weak security measures.
- Tag Cloning: Hackers can create duplicates of existing RFID tags, allowing them to gain unauthorised access to restricted areas or use cloned cards for fraudulent transactions. They can use specialised equipment to read the information stored on a legitimate RFID tag and then create an exact replica, which can be used to bypass security systems and gain access to restricted areas or even make unauthorised purchases. See also the case study here.
- Man-in-the-Middle Attacks: In this scenario, a hacker inserts themselves between the RFID tag and the reader, intercepting the communication between the two and potentially modifying the data transmitted. This type of attack can be used to manipulate data, such as changing the amount of a transaction or granting unauthorised access to a system.
- Denial-of-Service Attacks: Hackers can flood RFID readers with spurious signals, preventing legitimate tags from being read. This can disrupt operations and prevent authorised users from accessing systems or making transactions.
The Impact of RFID Hacking
RFID hacking can have a wide range of negative consequences, including:
- Identity Theft: Stolen credit card information can be used to make unauthorized purchases or open new accounts in the victim's name. The consequences of identity theft can be devastating, requiring significant time, effort, and resources to rectify.
- Financial Loss: Hackers can use cloned RFID tags to access bank accounts or steal funds from prepaid cards. Stolen funds can be difficult to recover, resulting in significant financial losses for individuals and businesses.
- Security Breaches: Unauthorized access to RFID-enabled access control systems can compromise physical security, allowing hackers to gain entry to restricted areas. This can lead to theft, vandalism, or even more serious security breaches, depending on the nature of the facility and the information stored within.
- Privacy Violations: RFID tags can be used to track individuals' movements and activities without their consent, raising serious privacy concerns. This type of tracking can be used for a variety of purposes, from advertising and marketing to surveillance and data collection, raising ethical and legal concerns about individual privacy and data security.
- Data Manipulation: Hackers can alter the data stored on RFID tags, potentially causing significant disruptions to businesses and critical infrastructure. This could include tampering with inventory records, manipulating supply chain information, or even compromising medical devices and systems.
How Can You Protect Yourself?
Fortunately, there are several steps you can take to mitigate the risks of RFID hacking. Here are some key strategies:
1. Use an RFID Blocking Card
An RFID Blocking Card is a simple and effective way to protect your cards from unauthorized scanning. This card emits a disruptive field that blocks RFID signals, rendering your cards invisible to scanners. Simply place the RFID Blocking Card in your wallet, and it will protect all of your credit cards, debit cards, and other RFID-enabled cards. It effectively disrupts the communication between your cards and RFID scanners, preventing hackers from accessing your sensitive information. No batteries or complex setup is required, making it an incredibly convenient and user-friendly solution.

2. Consider an RFID Blocking Kit
For a comprehensive approach, consider an RFID Blocking Kit, which provides a selection of RFID-blocking sleeves and cards for your wallets, passports, and other essential documents. Our RFID Blocking Kit offers an unbeatable value, providing a complete solution for protecting your sensitive information from RFID hacking. This kit typically includes a combination of RFID-blocking sleeves and cards, allowing you to protect a variety of items, from credit cards and passports to driver's licenses and even key fobs.

3. Be Aware of Your Surroundings
It's crucial to be mindful of your surroundings when you are using your RFID-enabled cards or carrying your passport. Try to avoid using your cards in crowded or unfamiliar places, as these areas may attract opportunistic RFID hackers. Be particularly vigilant in areas where you suspect RFID hacking may be a concern, such as public transportation hubs, crowded shopping malls, or even at concerts and festivals.
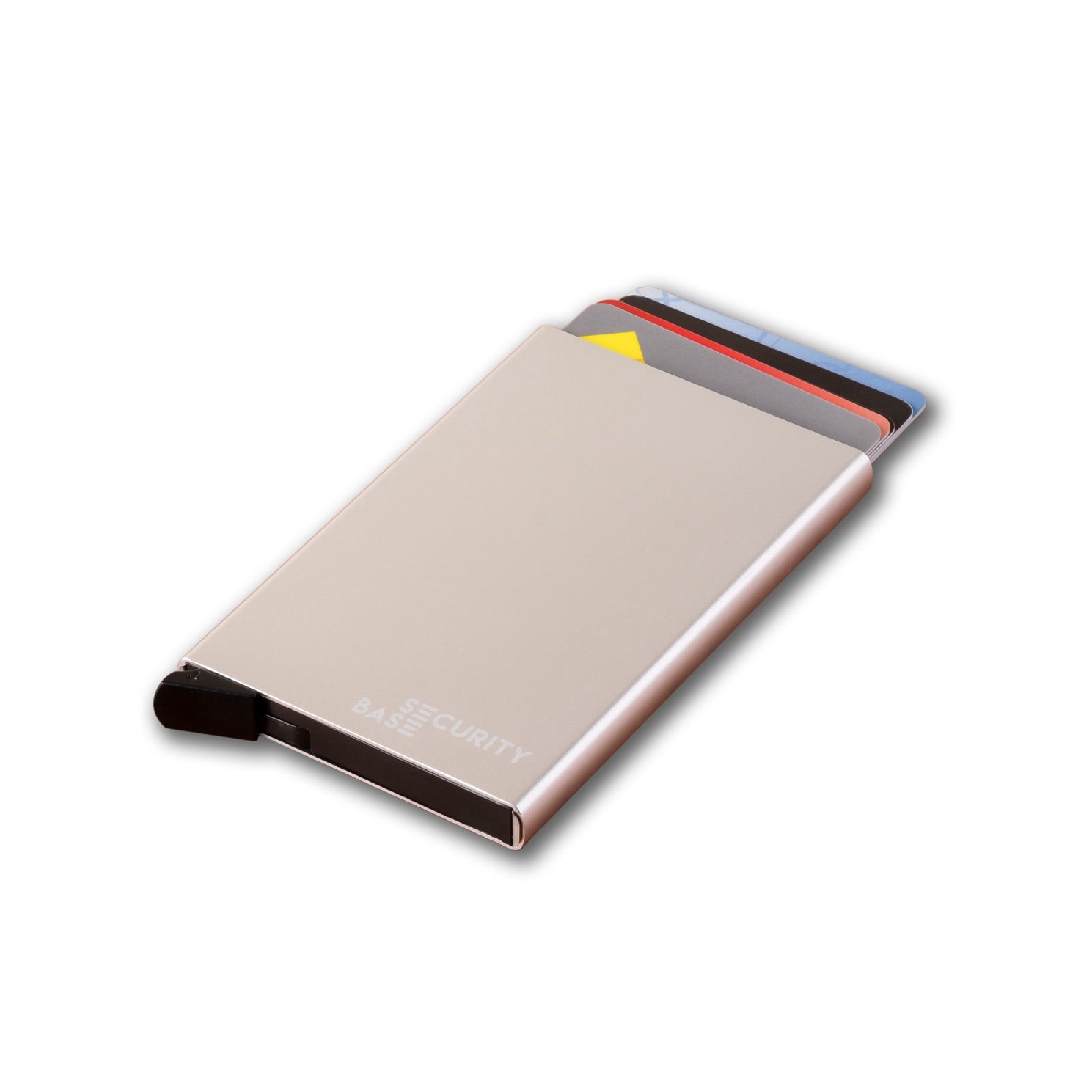
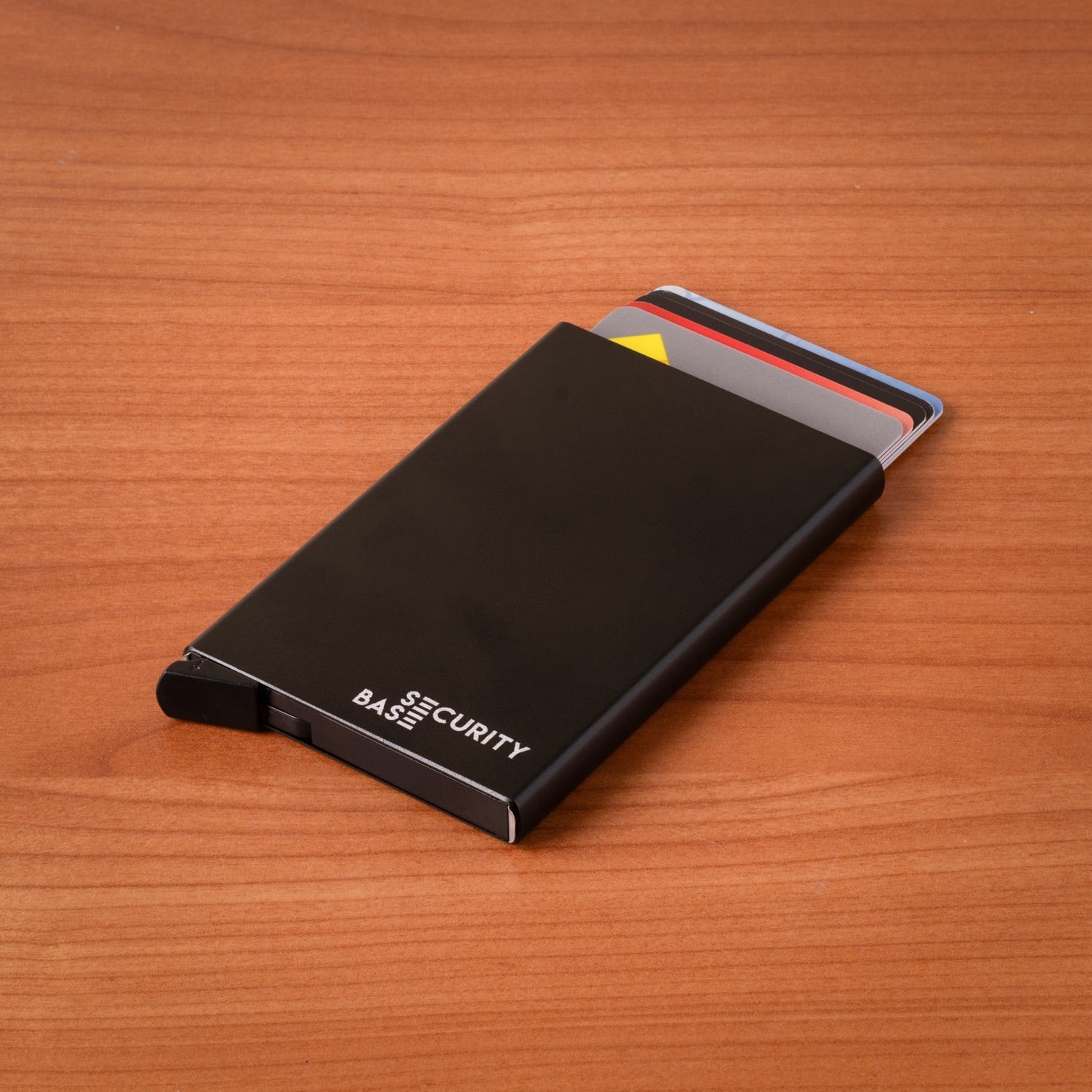
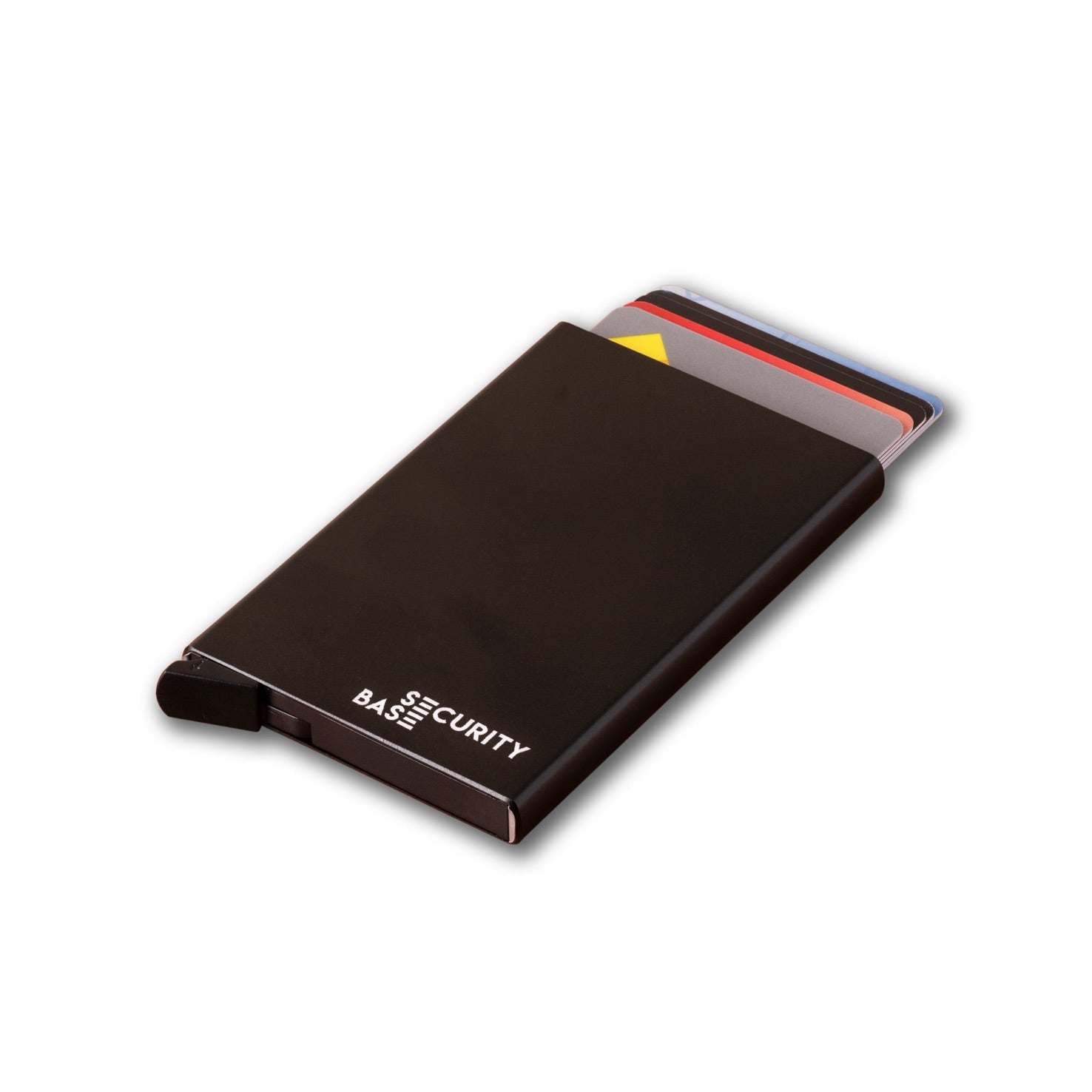
4. Use RFID-Blocking Wallets
Investing in an RFID-blocking wallet can provide an extra layer of security for your cards. These wallets are specifically designed with RFID-blocking materials to shield your cards from unwanted scanning. They often feature a built-in layer of Faraday cage material that effectively blocks RFID signals, protecting your cards from unauthorized access. Look for wallets made from materials like metal or specialized fabrics that offer RFID-blocking capabilities. Many manufacturers now offer stylish and functional wallets with RFID blocking features, so you can protect your cards without compromising on style.
5. Keep Your Software Up-to-Date
For devices that use RFID technology, such as smartphones and tablets, make sure to keep your software up-to-date. Software updates often include security patches that address vulnerabilities that could be exploited by hackers. By installing the latest updates, you can minimize the risk of your device becoming a target for RFID hacking. Regularly updating your software ensures that you have the latest security features and protections.
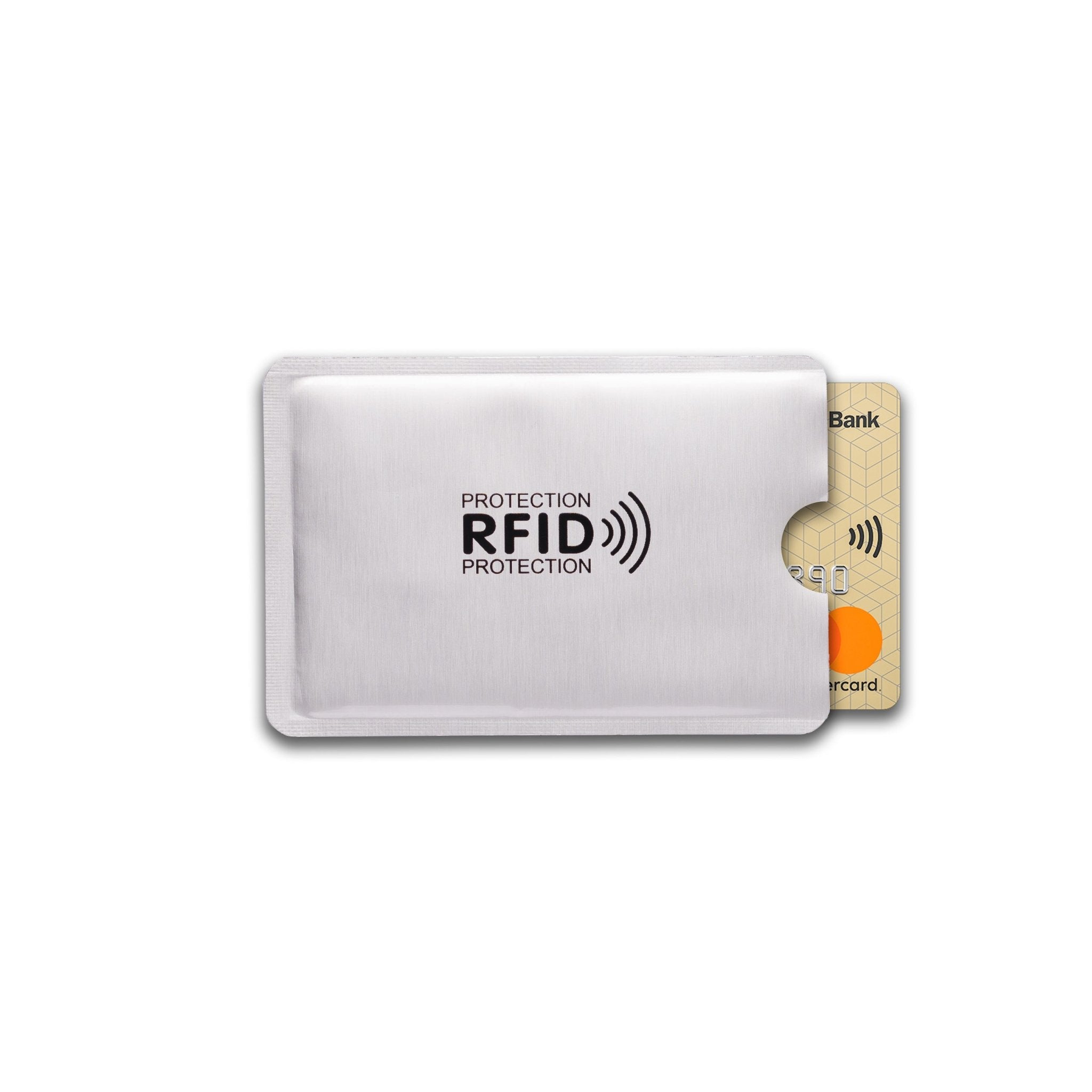
6. Consider RFID Blocking Sleeves
RFID blocking sleeves are another effective option for protecting individual cards. These sleeves are made from materials that block RFID signals, effectively shielding your cards from unwanted scans. They are particularly useful for protecting passports, driver's licenses, and other documents that may contain sensitive personal information. They are compact, lightweight, and easy to use, making them an ideal solution for everyday protection.
7. Minimize RFID Exposure
Whenever possible, try to minimize the amount of time your RFID-enabled cards are exposed. Keep your cards close to your body and avoid placing them on surfaces where they could be easily scanned. This simple precaution can help reduce the risk of unauthorized access.
8. Protect Your RFID-Enabled Devices
If you use RFID-enabled devices such as key fobs, access cards, or even vehicle transponders, consider protecting them from hacking attempts. You can do this by using physical shielding, such as a metal box or sleeve, or by applying specialized RFID-blocking tape to the device. This can prevent hackers from intercepting the signals emitted by the device and accessing the data stored within.
9. Be Cautious of Public Wi-Fi Networks
When using public Wi-Fi networks, avoid accessing sensitive information or performing online transactions that involve RFID-enabled devices. Public Wi-Fi networks can be vulnerable to hacking attempts, putting your data at risk. Consider using a virtual private network (VPN) to encrypt your internet traffic and protect your data from unauthorized access.
10. Use Strong Passwords and Authentication
If your RFID-enabled devices require passwords or PINs, ensure that you use strong passwords and authentication methods. Avoid using easily guessable passwords or default settings. Employ multi-factor authentication whenever possible to add an extra layer of security and make it more difficult for hackers to access your devices and data.
11. Report Suspicious Activity
If you suspect that your RFID-enabled devices or cards have been compromised, report it to the relevant authorities immediately. This could include contacting your bank, credit card company, or local law enforcement. Report any unusual activity, such as unauthorised transactions, unexplained charges, or unusual attempts to access your accounts.
Best way to prevent RFID hacking
As RFID technology continues to evolve and become more integrated into our lives, it's crucial to stay informed about the potential security risks and take steps to protect ourselves. By using RFID-blocking solutions like our RFID Blocking Card or an RFID Blocking Kit, and following the other tips outlined above, you can help ensure that your sensitive information remains safe and secure. By taking a proactive approach to RFID security, you can enjoy the convenience of this technology without compromising your privacy or financial security.