As technology continues to become a more significant part of our lives, so does cybercrime. Cybercrime costs individuals, businesses, and governments billions of dollars. The Australian Cyber Security Centre (ACSC) has received 13,500 reports in just three months, that's one reported cyber-attack every 10 minutes. The average damage is $ 2000 per individual and $ 2 million per business impacted. That is one cyber attack every 10 minutes.

Governments and security providers are doing what they can to stop these cybercrimes from happening. However, the number of victims and extent of financial, emotional and reputational keeps increasing.
What Is Cybercrime?
Cybercrime refers to any criminal activity that occurs online or on digital systems. It involves using a device (computer, smartphone, etc.) and a network. The device can serve as a crime source or the target. The network is the internet.
A cybercriminal's goal may be to access your personal (financial) information, sensitive business information, or use your system as part of a botnet. In general, there are two forms by which cybercrime happens, these are:
- Crimes in which computers or other IT devices are an integral part of an offence, such as identity theft, stealing of financial information or assets, cyberstalking and espionage.
- Computer or other technologies-related crimes that impact the functionality of a system, such as a virus, ransomware and DDOS-attacks.
How Is It Affecting Us?
The effects of cybercrime on Australian people and business is significant. Cybercriminals are targeting Australians to take advantage of their relative wealth and high adoption levels of technology. Banking, the use of government services, the activities on social media and all other online activities make us an attractive target for a cyberattack.
A cybersecurity review in 2019 revealed cybercrime costs the Australian economy 2 billion dollars annually. Another survey from 2018 shows, almost one out of three are Australian adults who were affected by cybercrime.
10 Types Of Cybercrime
There are several ways in which cybercriminals commit their crimes. To protect yourself, you need to understand how cyber criminals operate. The following are the ten most common types of cybercrime.
Fraud is a type of cybercrime that has the intent of deceiving an individual to gain access to (financial) information or assets. This fraud can involve the hiding of information or providing incorrect information to trick the victim. Fraud covers a range of illegal actions that are committed online, such as CEO-fraud, romance scams and the infamous "Nigerian Prince" e-mails.
Malicious Software (Malware) is used by cybercriminals to cause damage, suppress anti-virus software and other security, or use system resources such as memory. The goal is stealing information as well as disrupting the proper functioning of computer systems. The user can unknowingly download malware, which often disguises as a legit software. Unknowing to the user, the software contains a "Trojan horse" or spyware, which can cause significant damage to the system.
Ransomware is a type of cybercrime that proves to be one the most destructive. This type of malware gains access to your device, for example, trough a malicious e-mail attachment. It encrypts your files using military-grade encryption. The ransomware program displays a message demanding the user to pay a ransom for the decryption key to regain access to the locked information.
Phishing e-mails impersonate a legitimate sender, such as a well-known company or person. They often use a technique called spoofing, so it looks as if a legitimate sender sent the e-mail. The goal of a phishing e-mail is the extraction of information such as access codes for banking, passwords, credit card numbers, and so on.
Identity theft involves using someone else's identity to steal money or gain other benefits. Criminals can use your identity to purchase goods or services, take money from your bank accounts, apply for loans and other services in your name. Cybercriminals are especially interested in details such as your date of birth, address, drivers licence number, tax file numbers, passport information and medicare card details.
Cyberstalking is a relatively new type of crime. It involves (anonymously) following and contacting a person online. The cyber-stalkers harass their victim, for example, by making threats via e-mails, websites, social media, and discussion forums. The typical victims involved are women and children.
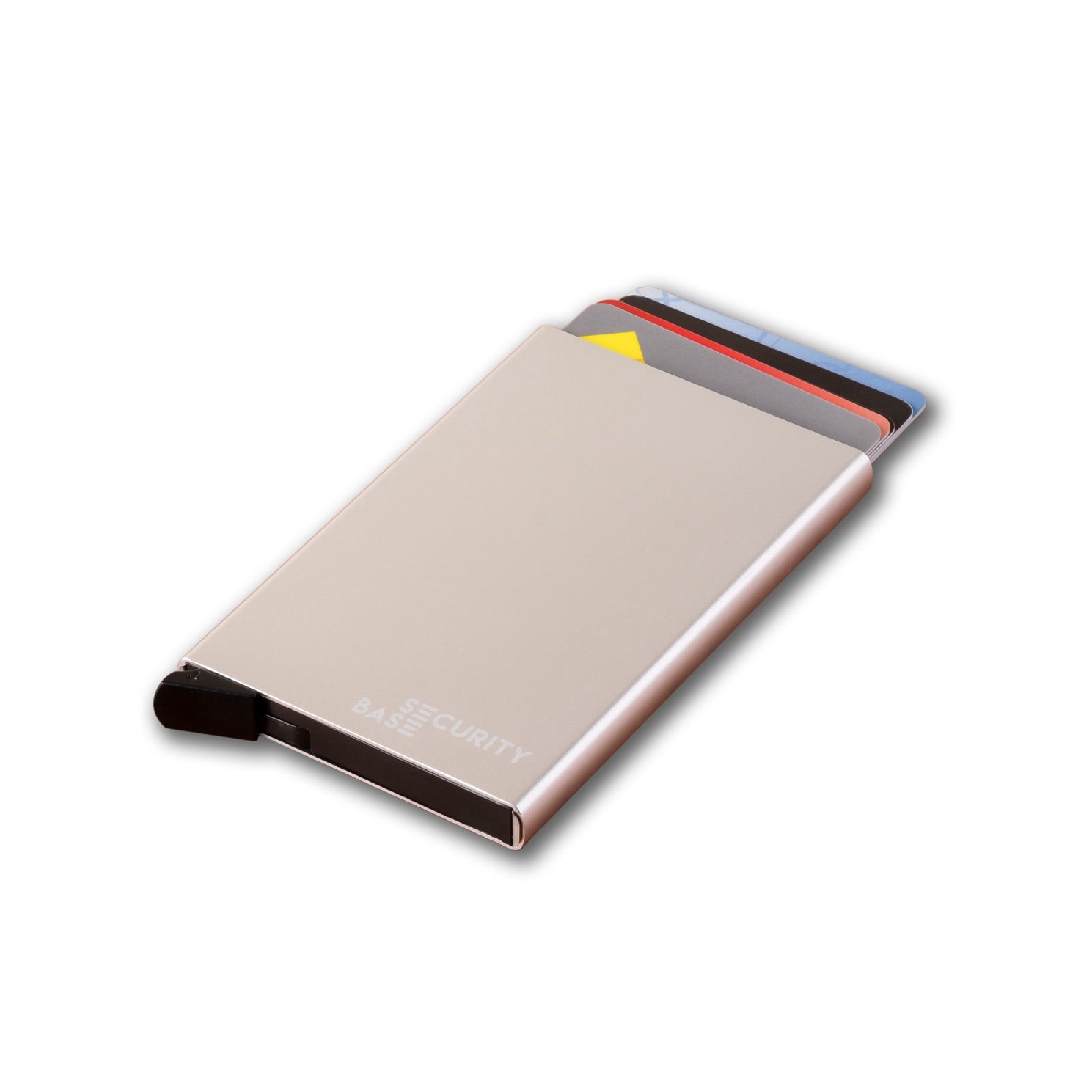
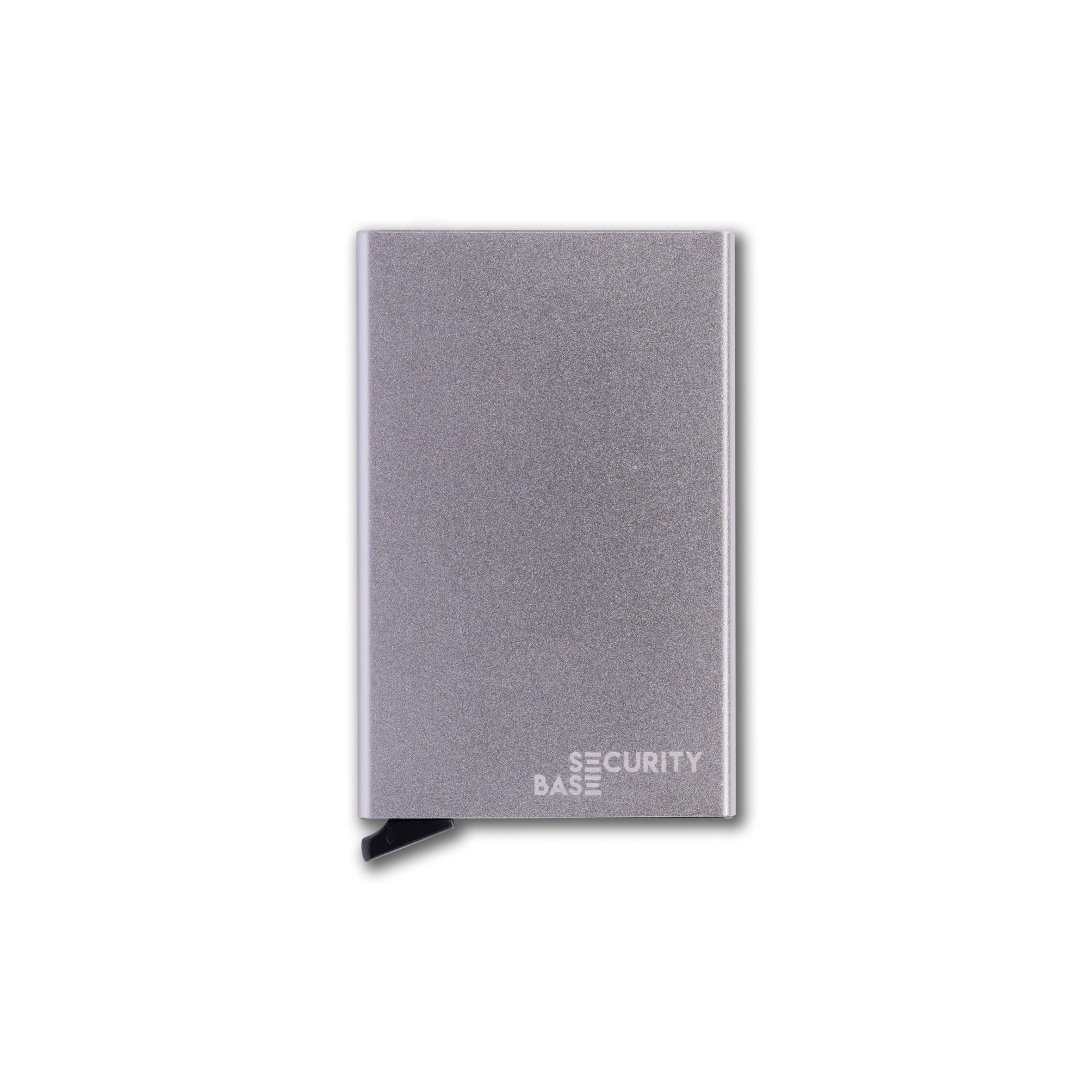
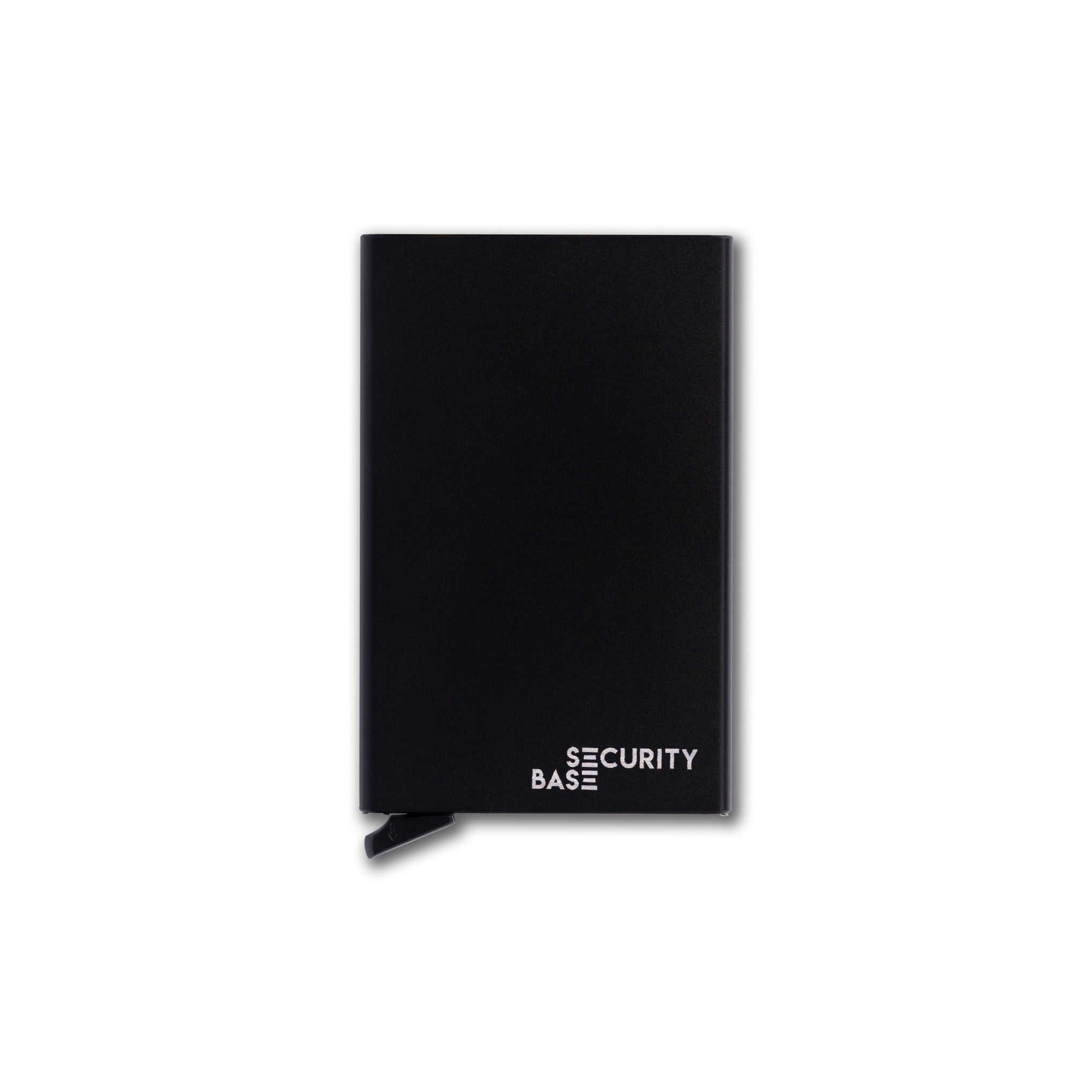
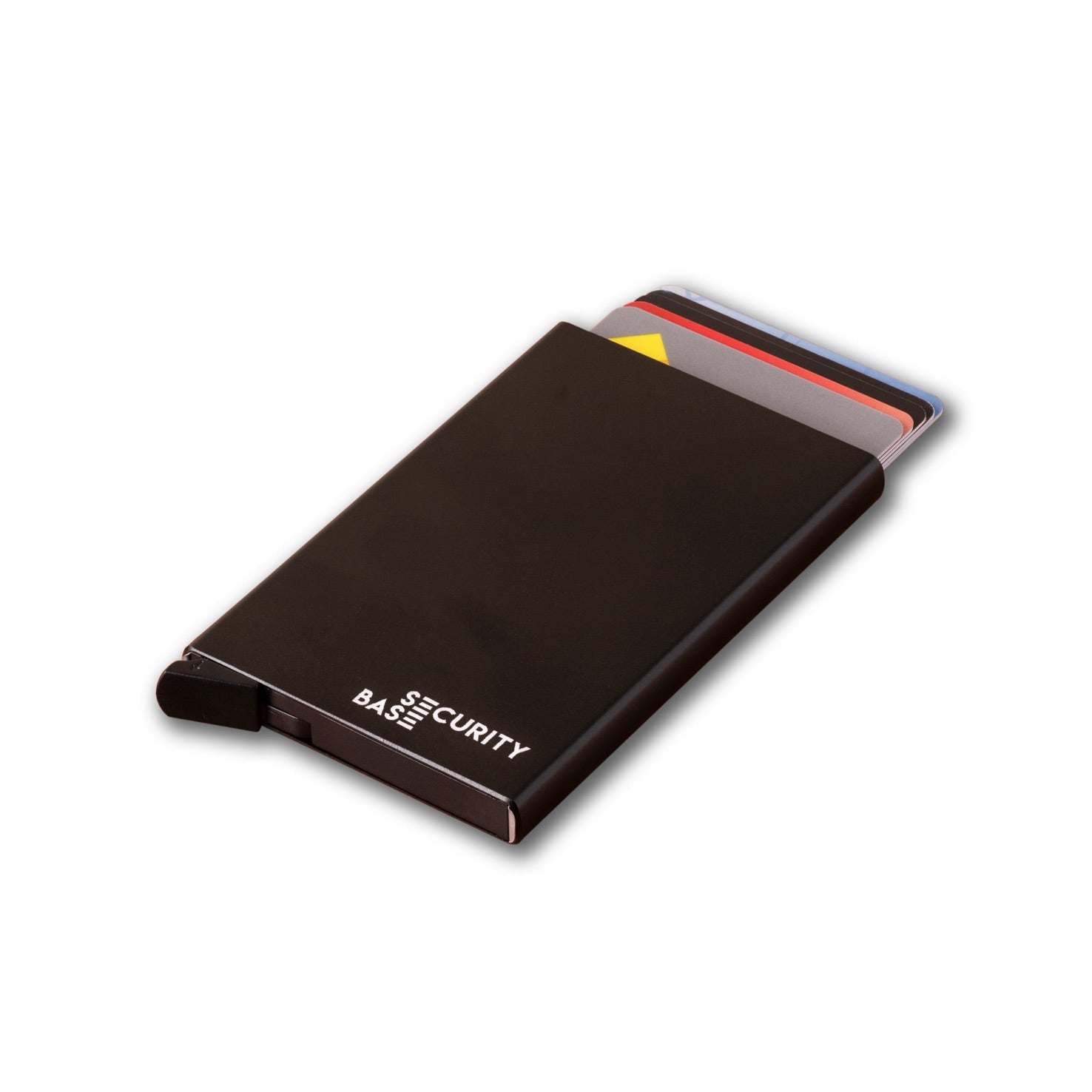
RFID Skimming, also known as digital pickpocketing is a relatively new type of crime. RFID stands for Radio Frequency Identification. This technology is used in credit cards, passports, access cards and many other products. Digital pickpockets can read details from your bank cards, passports and access cards by using RFID card readers. Even though this information is stored encrypted, decryption programs can make the information accessible for cybercriminals quite easily.
Juice-hacking is a type of cybercrime that primarily involves smartphones, tablets and other mobile devices. When you charge your device on a public USB-port, you might be connecting your device to a computer without knowing it. The "charging port" extracts data from the connected device or upload malware on it without you realising it.
Webcam extortion or sextortion is a form of cybercrime where a blackmailer threatens to share private images of you online unless you give in to their demand, such as paying a sum of money. The blackmailer uses intimate pictures that he or she has stolen through hacking your device. It also happens that a hacker accesses your webcam to take photos of you without you realising it.
Charity fraud is a form of fraud that is using the goodwill of people who believe they are making donations to charity. There are two types. Sometimes, a real charity is used to collect donations, but the money is not transferred to the charity. Other times, a fake charity is created to convince you to transfer your money to a charity that doesn't exist.
This is just a limited list of what can happen if you don't protect yourself. Other examples of cybercrime are DDOS attacks, botnets, dating or romance scams, espionage, software piracy, and many more. And then we have the dark web, where drug trafficking, child exploitation, and lively trade in stolen credentials and credit card details are happening. It also sounds scary, but you can protect yourself.
Understand the cyber risks by informing yourself using government websites such as staysmartonline.gov.au, subscribe to alerts from the Australian Cyber Security Centre and read our articles. Good cyber hygiene, some privacy tools, information security frameworks for businesses, and keeping yourself informed will help you to be safe online.